 In my very first post I've described PHP unserialize function and what are dangers of using it. During my research I've found out that Joomla has not sanitaze and validate serialized argument passing from request (CVE-2013-1453). Vulnerable code exists in Highlight system plugin which is enabled by default. Joomla 2.x and 3.x series are affected (<=2.5.8 and <=3.0.2), however 1.x is not vulnerable.
In my very first post I've described PHP unserialize function and what are dangers of using it. During my research I've found out that Joomla has not sanitaze and validate serialized argument passing from request (CVE-2013-1453). Vulnerable code exists in Highlight system plugin which is enabled by default. Joomla 2.x and 3.x series are affected (<=2.5.8 and <=3.0.2), however 1.x is not vulnerable.Exploitation with JStream class:
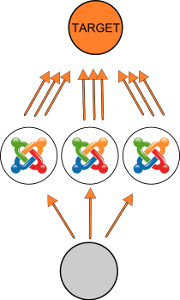
By using JStream class attacker can "chmod" any files with any mode with web server user, or use it to make connection (by ftp_connect function) to remote host. What is more, when we specify tcp port to 80 in connection string (ftp://u:p@host:80/), the php script will open connection which will last until php script time limit exceeded or connection to host is timeouted (because of differrent protocols). This can be used for DoS/DDoS attacks.
Video of using PoC exploit:
You can download exploit here.
PS. Cheers to Egidio Romano who found this bug week earlier than me and is credited in official joomla report :)